Gone in Six Seconds: How Hackers Break Into Your Network (And How QWERX Blocks Them)
Until recently, we believed that strong encryption could protect information because it took a long time to break encryption keys. For example, there were sophisticated operations, like Bletchley Park. Then someone stole the Enigma machine, and the world learned that stealing keys (and the machines that make the keys) is far more efficient and effective than trying to break them mathematically. Today, breaking encryption mathematically is more the domain of academics than criminal enterprises or the clandestine operations of governments.
In the realm of machine identity authentication, stealing credentials is the common attack vector. Trusted encryption key credentials are created that are associated with digital devices and are used to identify and certify the authenticity of a particular device. Therefore, the trusted credential becomes the initial target for the attacker as a means of gaining access to the targeted network.
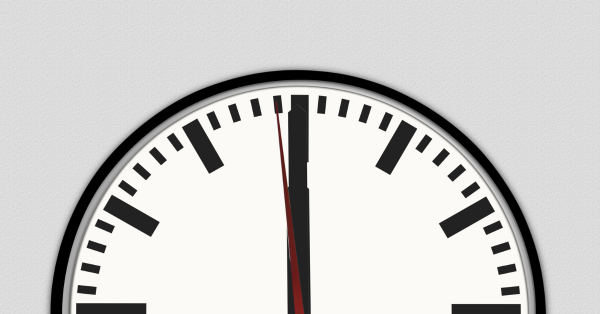
Attackers capitalize on a window of opportunity that may last as little as six seconds, opening when they launch the attack. This window is made up of four stages, as illustrated in the example below that follows a typical phishing or spear phishing attack:
- Launch of attack (.05 seconds): The clock starts when a target victim clicks a nefarious link. It takes about half a second for the click-through to connect the victim's device to the attacker's device.
- Obtaining credential (1 second): Assuming the attacker is efficient, it takes about a second for them to retrieve whatever credentials are stored on the target device.
- Use of stolen credential (5 seconds): The attacker turns the process around, logging off and logging back onto the target network using the credential they have just stolen
- Maintenance of connection (as long as permitted): The attacker may have to keep the window open longer to accomplish the goal of the attack, or they may wish to return later as long as they remain undetected.
The window of opportunity closes when the attacker is either denied access before gaining entry; discovered after entry and contained; or after a successful attack is completed.
If networks are using the recommended best practices from the US government and industry experts and using a 2056-bit credential and changing it every 30 days, the attacker now has a usable credential and access to your network until that credential expires. Depending on when the credential was last changed, the attacker has more than enough time to do whatever they wish inside a network. In the universe of cybercrime, even minutes are an eternity.
How QWERX Stops Attacks
QWERX fundamentally changes this vulnerability in two ways. First, QWERX credentials never exist anywhere in the system to be stolen. The constantly rotating, ephemeral keys are never stored in memory. Setting that aside for a moment, assume that the attacker somehow did manage to steal the current credential. Even in the slowest configuration, a QWERX credential expires in three seconds. In the fastest configuration it expires in a fraction of a second. That means that any credential that an attacker could acquire would be replaced before the attacker could exploit it to penetrate the target network.
If you'd like to learn more about how QWERX technology can eliminate unauthorized access to your networks, click here to contact us.


